Biggest Cyber Attacks, Data Breaches, Leaks and Hacks of 2016
Cyber attack results show over 2.2 billion records stolen

It’s time to reflect on some of the most audacious, embarrassing and dangerous hacks, leaks and data breaches from the past year. 2016 is finished but and at this point there have been more than 2.2 billion records stolen in the past 12 months with a large number coming from historical breaches.
“Five hundred of the Fortune 500 have been hacked,”. “If anything has changed, it’s that these attacks are getting publicly disclosed.” said Dan Kaminsky, Chief Scientist of White Ops, a firm specializing in detecting malware activity via JavaScript.
Here are some of the largest hacks from 2016
Yahoo – Yahoo has advised they have had at least an incredible 500 million accounts compromised. The intrusion actually happened in 2014 but was only picked up by the company in August of 2016 following an investigation into a separate breach. The August cyber attack turned out to be false but brought to light the extent of the 2014 intrusion. While Yahoo says the information taken was low-value data it did include security questions and answers which would make users vulnerable if used across multiple sites.
Linux Mint backdoor – The Linux operating system still remains one of the most popular Linux releases with approximately 6 million users despite a recent backdoor being announced. The malicious code was inserted into the legitimate version listed on the official Linux Mint forums. Hundreds of users downloaded the malicious build before detection.
“The hacked ISOs are hosted on 5.104.175.212 and the backdoor connects to absentvodka.com. Both lead to Sofia, Bulgaria, and the name of 3 people over there. We don’t know their roles in this, but if we ask for an investigation, this is where it will start.” said the official Mint statement.
SWIFT – SWIFT or Society for Worldwide Interbank Financial Telecommunication is a global organisation that operates a trusted and closed computer network for communication between member banks around the world. With 11,000 members and around 25 million financial messages sent per day SWIFT is a prime target for a cyber attack. On February 4, 2016 unknown hackers used Bangladeshi Bank employee SWIFT credentials to send approx $850 million to numerous accounts in the Philippines, Sri Lanka and other parts of Asia.
When Bank employees found the error $81 million had already been credited to multiple accounts—reportedly belonging to casinos in the Philippines—and all but $68,000 of it was withdrawn on February 5 and 9 before further withdrawals were halted. The hackers might have stolen much more if not for a typo in one of the money transfer requests that caught the eye of the Federal Reserve Bank in New York.
TRUMP – The president elect’s TRUMP hotel chain has been the victim of two cyber attacks since 2015 with the most recent in April 2016. According to some sources the organisation was using unpatched and insecure systems which were more than 10 years old. The April findings were only scratching the surface but it is likely the TRUMP organisation has been compromised much further.
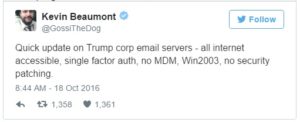
Then, Trump’s presidential campaign leaked the resumes of prospective interns, including their names, addresses, and in some cases sensitive employment details. Let’s hope his cybersecurity strategy is better when he’s in office.
Insure your business against a cyber attack, Get a free quote today!
LinkedIn – The global professional networking company was first compromised in 2012. As with the same case as Yahoo, the scale of the historical 2012 breach was only understood this year when the number of stolen accounts exploded to almost 117 million. One reporter noted that the majority of stolen accounts had passwords found in the annual worst passwords list from SplashData.
The alleged hacker was eventually caught in the Czech Republic.
Here’s how to check if your accounts have been compromised in a cyber attack, haveibeenpwned.com
Tumblr – It comes as no surprise that the Yahoo owned micro blogging and social networking website, Tumblr suffered a similar breach to their parent company in 2013 before the acquisition. Tumblr staff announced that it had been the victim of a security breach but refused to give details until investigative journalists discovered the stolen database had more than 65 million accounts.
MySpace – Formally the world’s largest social network, Myspace suffered their largest known exploit and brought them back into the headlines for the wrong reasons. The breach occurred on June 11th, 2013 but once again was only fully recognised earlier this year after further investigation.
“Each record may contain an email address, a username, one password and in some cases a second password.The methods MySpace used for storing passwords are not what internet standards propose and is very weak encryption or some would say it’s not encryption at all but it gets worse. We noticed that very few passwords were over 10 characters in length (in the thousands) and nearly none contained an upper case character which makes it much easier for people to decrypt.” said leaked data analysts at leakedsource.com.
US Political Attacks – The media had a field day surrounding the 2016 US election accusations from the White House that the Kremlin had committed politically motivated hacks on presidential candidates. Director of National Intelligence, James Clapper stated that “based on the scope and sensitivity of these efforts, that only Russia’s senior-most officials could have authorized” regarding the hacks. Russia has repeatedly denied the hacking allegations.
“Either stop talking about it or finally provide some evidence. Otherwise it looks indecent,” Kremlin spokesman Dmitry Peskov told reporters in Tokyo.
VK – The largest European online social networking service, based in Russia was the victim of 3 separate hacks in as many months. According to reports, the attack occurred in 2012 or 2013 and continues the historical hack trend which has dominated this list. An estimated 171 million accounts from VK.com and their parent company Mail.ru’s forums.
The hacker is now reported to be selling a portion of the database. 100 million accounts, which turns out to be a little over 17 gigabytes in size have been found on a dark web marketplace for 1 bitcoin.
NSA – The infamous National Security Agency which is an intelligence organization of the US government, responsible for global monitoring, collection, and processing of information and data for foreign intelligence and counterintelligence purposes has had their internal tools stolen and auctioned off by The Shadow Brokers.
The hacking tools which could break through Fortinet and Cisco firewalls was seen listed for auction through known exploit sites. With the wide range of Snowden Leaked files sources are able to confirm that the exploit tools belonged to the US government.
At the time of writing the auction has failed however, The Shadow Brokers have now appeared to have put up the NSA’s hacking tools and exploits for direct sale on an underground website.
NSA 2nd breach – To add to the public woes the NSA has been dealing with over the past three years, Harold Martin, former staffer stole approximately 50 terabytes of data from the the United States’ top security organisation. The majority of the information taken was considered classified and actually greatly eclipsed the previous breach by Edward Snowden.
Martin has been initially charged with mishandling information which has now been upgraded to espionage. While a lot of information was classified there is a large amount which is of greater public interest for which Martin has done a great service. Martin reportedly simply walked out the front door with the data over the course of his 20 year employment. This is case study number 1 for future employee breaches.
Oracle Point-of-Sale Terminals – Point of sale machines have become common place globally to assist all business’s process and retain important customer details. Micros, one of the largest terminal manufactures which was acquired by Oracle in 2014 for $5.3 billion reported that “hundreds of systems” at the company had been compromised.
The compromised systems had malware installed which was designed to remotely access usernames and passwords from systems located in retail outlets internationally.
Weebly – The web development and design giant put more than 43 million customers at risk earlier this year thanks to their own terrible internal security.
Weebly has openly admitted in a statement that the security gap and cyber attack was their own fault and they are taking appropriate measures for future security. The hacker reportedly took records which included usernames, passwords, IP addresses and email addresses.
AdultFriendFinder – The 2015 Ashley Madison breach which involved approx 37 million accounts has been made to look like a drop in the ocean after the 2016 AFF breach.
More than 400 million users were exposed in a targeted attack on the AdultFriendFinder network. The adult hook-up website has reportedly compromised an absolutely staggering 20 years of data from their initial set up in 1996. AdultFriendFinder describes itself as “one of the world’s largest sex hook-up” websites, with more than 40 million active users and a handful of similar adult oriented sites which were also compromised.
In the cyber attack stolen data included usernames, browser information, date of the users last visit, purchasing patterns and more.
Insure your business against cyber crime.
Conclusion
Many more breaches have occurred which did not make the above list and with the enormity of the historical breaches now being brought to public attention it looks like 2017 is set for bigger and scarier reports to surface.
“I’m afraid we no longer live in a world where you can prevent breaches taking place, instead it is about how you manage them and what measures you have in place to protect your business and importantly, your customers. As recent events have shown, hard-earned reputations can be lost in a flash if you do not have the correct plans in place.” Inga Beale, Lloyd’s Chief Executive.


Comments
Not found any comments yet.